POSTED ON 02 AUG 2016
READING TIME: 5 MINUTES
Approaches to infrastructure and application management - part 2
In the previous post about common approaches to customer infrastructure and application management we’ve briefly introduced the concept of federated monitoring. Now it is time to dive deeper.
The federated approach is an architecture characterized by:
- A “master-slave” arrangement in which the network management and application monitoring function is split between the client (“slave”) and the MSP premises (“master” or “umbrella”). The master/umbrella system also contains the Service Desk & SLA management for internal MSP use providing a “single pane of glass” view of the entire managed infrastructure.
- A single tool for business-oriented, cross-silos management & monitoring of networks, data centers, applications and clouds for the client, rather than a number of separate tools.
 Federated infrastructure and application management (MSP perspective)
Federated infrastructure and application management (MSP perspective)
What are the benefits of the federated monitoring architecture?
Business service orientation
The typical MSP offering is usually infrastructure-focused (networks, hardware and basic operating systems). These elements, however, are seen by CEOs and CFOs on the cost side rather than the revenue generation side.
For instance, for a manufacturing company the ERP system is their focal point as it leads to revenue generation, the hardware and network are only a platform to keep the production running.
Monitoring solution must be able to reflect how C-level management views their IT, i.e. as a collection of business services, for instance:
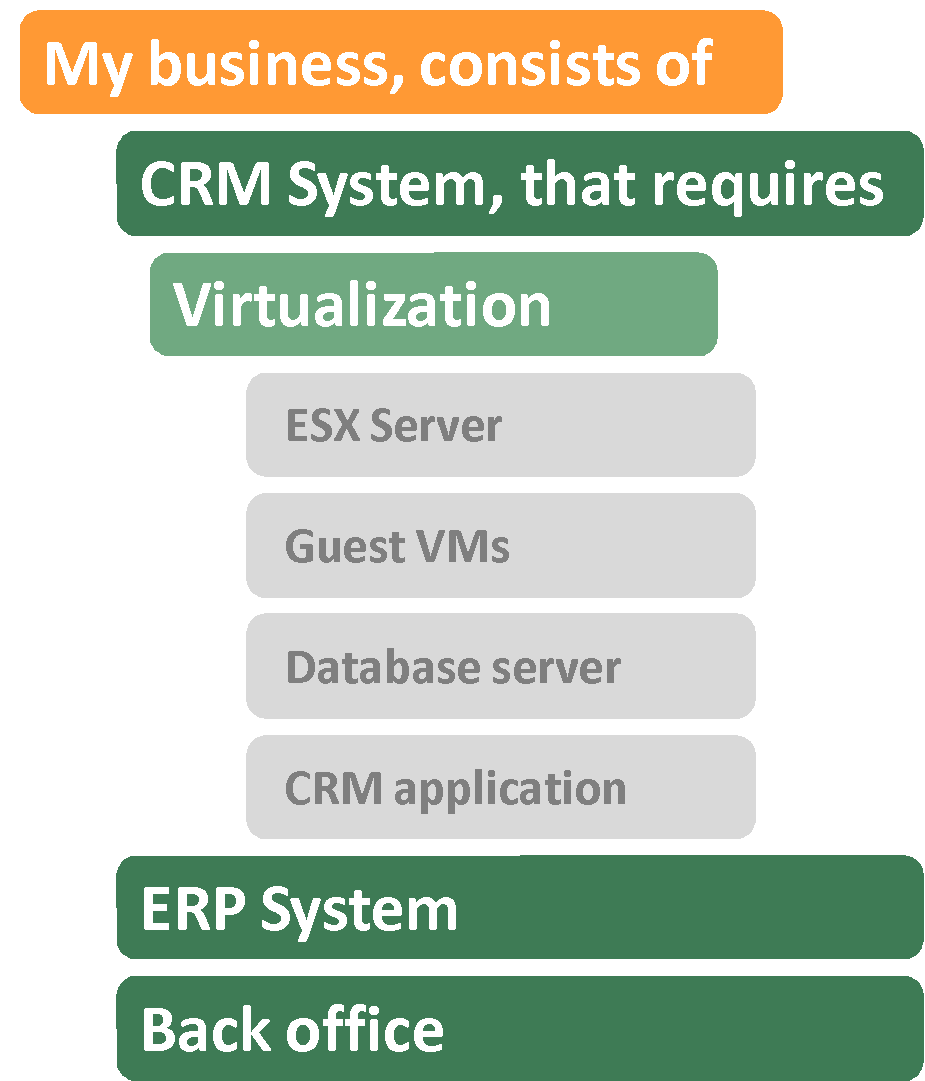
Management views on IT infrastructure
The federated management approach not only provides the detailed visibility on how IT outages impact the business via end-to-end business process monitoring, but also enables root cause analysis from hardware through application to business functions in a single system.
Reports and demonstrating business value
The area, where the MSP often fail is in reporting their value to the end customers. Because of the service-orientation, the federated approach allows MSPs to not only report data useful to systems administrators (e.g. top 10 failing devices, number of alarms), but also report how the business as a whole is performing.
This enables MSPs to create business oriented SLAs in addition to infrastructure oriented SLA’s. This reflects the thinking of management, e.g. what was the IT impact on the business side of things. For organizations that IT has a large impact on, reducing downtime brings significant savings. If MSPs can demonstrate the direct relationship between revenues and their activities, they are more likely to build a lasting business relationship with their clients.
Mixed MSP/own IT staff approach
Medium and large clients may be reluctant to rely completely on an MSP to manage their infrastructure. Similar to private clouds which extend existing infrastructure, MPSs are often brought in to complement or extend their clients existing IT teams. The federated approach allows for mixing of internal/MSP staff in a very flexible manner, e.g. 8AM-5PM workdays is the time that the clients internal staff is responsible for, weekends and nights for the MSP. It also mitigates risk from the MSP customer’s stand point and allows for gradual transition of responsibility from in-house IT staff to the MSP.
IT automation
Location of the NMS & APM within the MSPs management domain is also advantageous for IT automation scenarios such as “restart a guest virtual machine from VMware ESX level when response times are too long” – as they are less risky without latencies and dependence on a WAN link between the MSP and their client. This approach is more “firewall-friendly” than trying to achieve same from a remote system.
Bandwidth preservation
When a local monitoring system is used, a large proportion of the data is stored locally. This approach is beneficial for MSPs since the bandwidth required between MSPs and their clients is lower. In addition, the MSP needs fewer resources to service multiple clients. The master system stores limited event data only.
Resilience to failures
The proposed architecture is resilient to MSP’s infrastructure failures and interconnectivity problems:
- If MSP infrastructure has downtime, the data (e.g. network performance, outages) is still collected locally. Notifications can still be sent from local NMS & APM system to MSP personnel ensuring service continuity.
- The same applies to a situation when ISPs WAN link between MSP and the client is down. In this scenario, it is also feasible to support out-of-band communication with the umbrella system with causal information.
- If a local NMS & APM system goes off-air, the master NMS & APM immediately notices such situation and MSP personnel can take immediate action to bring it on line.
Moreover, for a local NMS & APM system a Fault Tolerant (FT) installation of the NMS & APM is available.
Single NMS & APM instance for unified network and application management
When local NMS & APM managers are present, the MSP’s Master NMS & APM working as their umbrella system can be considerably smaller in:
- Number of instances (the client uses their own NMS & APM to view current performance, and does not need to have remote access to MSP’s master system.).
- Number of licenses for managed elements (one client’s slave NMS & APM is equivalent to a single managed entity).
- No need for separation of data, multi-user access or multi-tenancy on MSP side – the clients have local access to their data.
All of these factors mean less investment into the MSPs management platform. It also means independence of upgrade of the MSP system.
How does it work in real environment?
If you want to see how federated approach works in a real-life scenarios - sign up for one of our live demonstration sessions where our technical team will guide you thru its basic concepts and demonstrate how you and your clients can simplify and automate IT infrastructure management.